One of the decisions you may have taken when you first planned on your Azure AD/ Entra ID sync was the UPN and what it will be. The recommendation from Microsoft is to always align the Entra ID UPN with the user’s email address. Why you ask? It is mainly to avoid confusion among the users. They simply know their Email address but if the helpdesk asks what is your User Principal Name from the user, they will have no answer.
Aligning the Entra ID UPN to the email address
UPN: jbloggs@yourdomain.com
EMAIL: jbloggs@yourdomain.com
While this is the recommendation, there are situations where you can’t align both to be the same. For example, It can be due to a management decision, changes in domains or AD domain, and the email address domain names are different.
Not to be confused with the options in Azure AD Connect Sync tool
This is not what’s presented in the Entra ID Connect (Azure AD Connect) tool’s User Principal Name section.
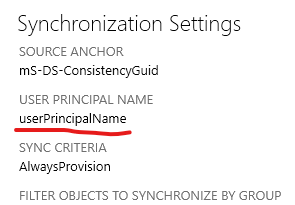
During the Azure AD Connect setup, it will ask you to select which attribute from the On-Premises AD to be taken as the Entra ID username and there is a drop-down list as below.

Usually, selecting the userPrincipleName is a good practice because there can be users without email addresses in some cases, but they all have a login ID.
This userPrincipalName directly correlates with the User logon name in the AD user property. To refresh your memory, this is where you select a routable UPN if your AD domain name suffix is not a routable domain.

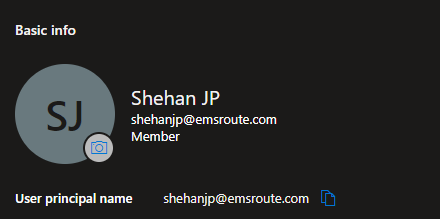
Once this is synced with Entra ID, the user’s Entra ID account UPN will be set as below.
But if the company uses the Email as the UPN, then the Entra Connect tool needs to have the Email as the User Principal Name from the drop-down.
Ok this we know, so what’s new?
Microsoft has finally announced the flexibility of using the email address as an alternative to the UPN. This address can be the Primary SMTP or a proxy address. This gives the end user some flexibility as well as a backup method to login as well.
This feature is still in Preview at the time of writing.
Another benefit can be the end user login to another application or a service that is registered with the alternate address, for that type of scenario, there is nothing to be forced and the user can still use the alternate login ID.

Preview Limitations
Since this is still the preview, there are some limitations and Microsoft has elaborated them here
Some Need to know stuff before you start (Straight from Microsoft Learn)
- The feature is available in Microsoft Entra ID Free edition and higher.
- The feature enables sign-in with ProxyAddresses, in addition to UPN, for cloud-authenticated Microsoft Entra users. More on how this applies to Microsoft Entra business-to-business (B2B) collaboration in the B2B section.
- When a user signs in with a non-UPN email, the
unique_nameandpreferred_usernameclaims (if present) in the ID token will return the non-UPN email.- If the non-UPN email in use becomes stale (no longer belongs to the user), these claims will return the UPN instead.
- The feature supports managed authentication with Password Hash Sync (PHS) or Pass-Through Authentication (PTA).
- There are two options for configuring the feature:
- Home Realm Discovery (HRD) policy – Use this option to enable the feature for the entire tenant. Global Administrator, Application Administrator, or Cloud Application Administrator role is required.
- Staged rollout policy – Use this option to test the feature with specific Microsoft Entra groups. Global Administrator privileges required. When you first add a security group for staged rollout, you’re limited to 200 users to avoid a UX time-out. After you’ve added the group, you can add more users directly to it, as required.
How to Enable the feature?
Make sure the Proxy Address domain is verified in Entra ID.
Synchronize Sign-in Email address (ProxyAddresses) attribute to Entra ID.
During preview, you currently need Global Administrator permissions to enable sign-in with email as an alternate login ID. You can use either Microsoft Entra admin center or Graph PowerShell to set up the feature.
With the policy applied, it can take up to an hour to propagate and for users to be able to sign-in using email as an alternate login ID.
Since this is still in preview, you can start by a staged roll out and if it’s working as expcted, enable it to the whole tenant.
Staged Rollout using an Entra ID Group
Permissions required: Global Administrator
Install-Module AzureADPreviewIf prompted, select Y to install NuGet or to install from an untrusted repository.
Sign in to Microsoft Entra using the Global Administrator
Connect-AzureAD
List all existing staged rollout policies using the following cmdlet:
Get-AzureADMSFeatureRolloutPolicy
If there are no existing staged rollout policies for this feature, create a new staged rollout policy and take note of the policy ID:
$AzureADMSFeatureRolloutPolicy = @{
Feature = "EmailAsAlternateId"
DisplayName = "EmailAsAlternateId Rollout Policy"
IsEnabled = $true
}
New-AzureADMSFeatureRolloutPolicy @AzureADMSFeatureRolloutPolicy
Find the directoryObject ID for the group to be added to the staged rollout policy. Note the value returned for the Id parameter, because it will be used in the next step.
Get-AzureADMSGroup -SearchString "Name of group to be added to the staged rollout policy"
Add the group to the staged rollout policy as shown in the following example. Replace the value in the -Id parameter with the value returned for the policy ID in step 4 and replace the value in the -RefObjectId parameter with the Id noted in step 5. It may take up to 1 hour before users in the group can sign in to Microsoft Entra ID with email as an alternate login ID.
Add-AzureADMSFeatureRolloutPolicyDirectoryObject -Id "ROLLOUT_POLICY_ID" -RefObjectId "GROUP_OBJECT_ID"
For new members added to the group, it may take up to 24 hours before they can sign in to Microsoft Entra ID with email as an alternate login ID.
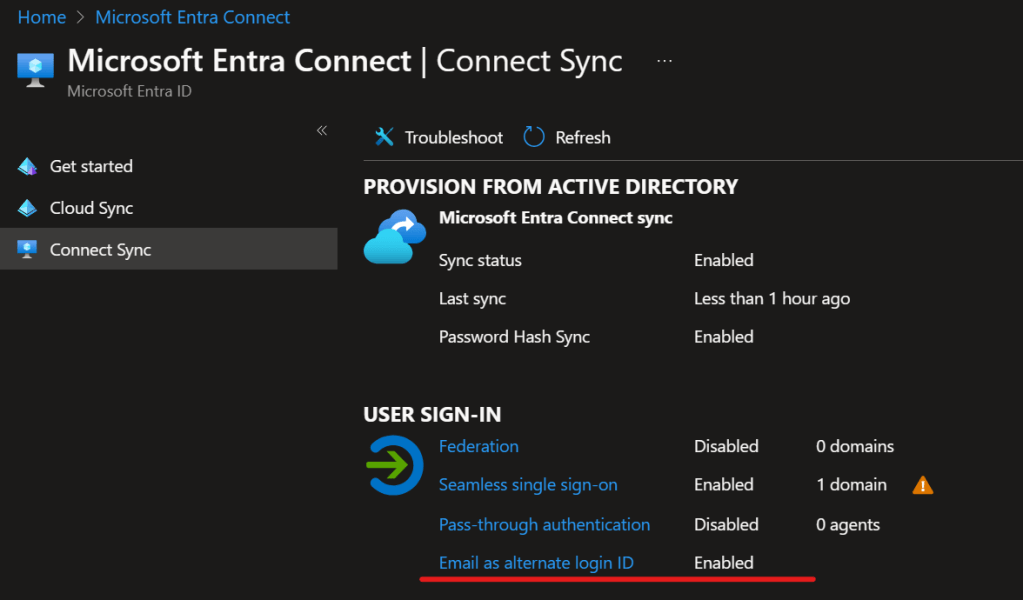
How to set it up using the Entra ID portal for the whole tenant
entra.microsoft.com > Identity > Hybrid Management > Microsoft Entra Connect > Connect Sync

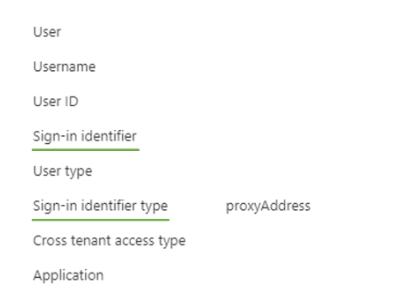
Checking Sign-on Logs
This is important to underatand how the user have logged in and using which ID.
Curently with the preview, it will not show the UPN and the Sign-in identifier info accurately.

However, it will show the details as below once its all out
What about in B2B Scenarios? (From Microsoft text)
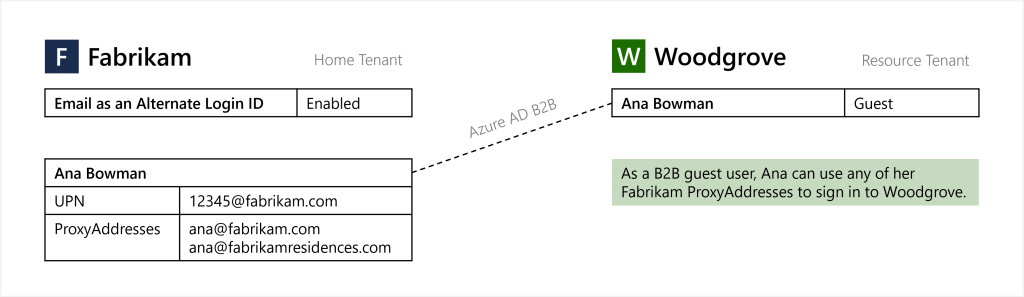
Email as an alternate login ID applies to Microsoft Entra B2B collaboration under a “bring your own sign-in identifiers” model. When email as an alternate login ID is enabled in the home tenant, Microsoft Entra users can perform guest sign in with non-UPN email on the resource tenant endpoint. No action is required from the resource tenant to enable this functionality.
Wrapping Up
This is a much needed option according to my understanding, This gives flexibility to organizations so they can use other IDs (Proxy addresses) that goes along with their policies.
Discover more from EMS Route
Subscribe to get the latest posts sent to your email.
